Zero-Interaction Authentication Method Doesn't Need Password For Secure Login
The new method of zero-interaction authentication works a lot like the passive 'keyless entry' system that is becoming popular in cars. It lets user access a PC, tablet or a car without interacting with it. Using wireless channels such as Bluetooth, the system detects the user’s security token such as a mobile phone and then depending on it, verifies and grants access to the user. This works the same way as the BlueProximity app - that can be used for automatically locking and unlocking the screen when you and your phone leave/enter the desk.

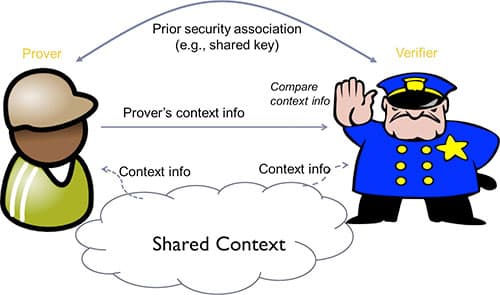
Before we go on to label this new mechanism as a plain proximity detector, we have to consider the fact that the zero-interaction authentication in use today are vulnerable to relay attacks (also called "ghost-and-leech attacks"). These attacks normally have a hacker or ghost who authenticates to the terminal on behalf of the user by colluding with another hacker or leech, who is close to the user at another location.
To counter such attacks, the UAB research team studied two types of sensor modalities - First included four sensor modalities that are commonly present on devices: Wi-Fi, Bluetooth, GPS and audio and Second involved the capabilities of using ambient physical sensors as a proximity-detection mechanism and focused on four: ambient temperature, precision gas, humidity and altitude. The second method was clearly a winner. By employing multiple modality combinations, the researchers were successful in delivering a robust relay-attack defense as well as good usability.