Wireless Devices & Apps Used By Casual Pilots For Data & GPS Vulnerable To Security Attacks
@abrakadabra
•
Oct 26, 2024
Oct 26, 2024
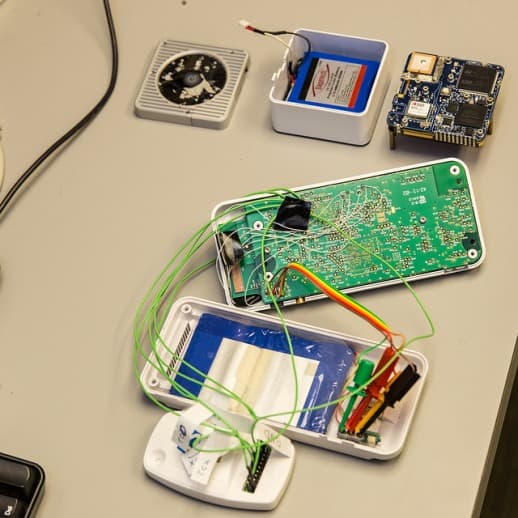
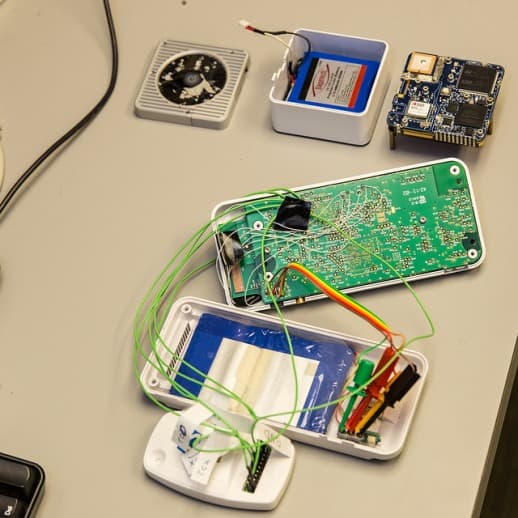
1.6K
Researchers from University of California, San Diego Jacob School of Engineering and Johns Hopkins University have teamed up to present a study that shows how the wireless devices and apps used during private flights by casual pilots are vulnerable to a number of security attacks. The engineers & computer scientists were able to showcase how attackers could access & manipulate safety-critical real-time information to cause severe harm to the flight, only because several secure design practices were not followed while designing them. To demonstrate their findings, the researchers used a combo of apps & devices generally used by private pilots. These include the Garmin GDL 39 receiver-Garmin Pilot app, the Appareo Stratus 2 receiver-ForeFlight app (one of the top grossing apps on App Store) and the SageTech Clarity CL01-WingX Pro7 app.

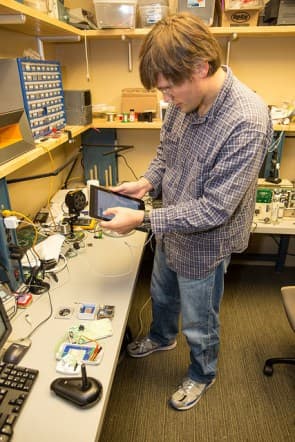
These devices are usually paired with iPads (or other tablets) to display the information for the casual pilots. This information generally includes data about the weather, current position, direction indications, airspace restrictions and the location of nearby aircrafts. During their study, the computer scientists found that all there combinations of wireless devices and apps had significant safety loopholes. For instance, two of the systems can allow the attacker to completely replace the firmware or downgrade it, which means the attacker could gain control of the program that operates these devices. Moreover, all the three aforementioned devices let the hacker/attacker meddle with the communication between receiver and tablet.
This just goes on to say that if attacked, the results could be disastrous. For example, if the pilot receives incorrect aircraft position on his tablet during flight in poor weather conditions, it could collide with another aircraft or crash down. The researchers went on to propose the different practices that can be followed for secure design of the apps and wireless devices used by casual pilots. Some of them are - using cryptography to secure communication between the tablet and the receiver and pairing them, requiring user acknowledgement before updating firmware, downloading of data such as maps & location using HTTPS or digitally signatures by the vendor.
We could only hope that the developers of these systems are taking note and performing the necessary measures required to secure these vital systems for casual pilots. Interested people can take a look at the <a href="https://cseweb.ucsd.edu/~savage/papers/CCS14MobileCockpit.pdf" target="_blank" rel="noopener noreferrer">PDF</a> submitted by the team. What are your thoughts on the new study? Share with us in comments below.
Source: #-Link-Snipped-#

These devices are usually paired with iPads (or other tablets) to display the information for the casual pilots. This information generally includes data about the weather, current position, direction indications, airspace restrictions and the location of nearby aircrafts. During their study, the computer scientists found that all there combinations of wireless devices and apps had significant safety loopholes. For instance, two of the systems can allow the attacker to completely replace the firmware or downgrade it, which means the attacker could gain control of the program that operates these devices. Moreover, all the three aforementioned devices let the hacker/attacker meddle with the communication between receiver and tablet.
This just goes on to say that if attacked, the results could be disastrous. For example, if the pilot receives incorrect aircraft position on his tablet during flight in poor weather conditions, it could collide with another aircraft or crash down. The researchers went on to propose the different practices that can be followed for secure design of the apps and wireless devices used by casual pilots. Some of them are - using cryptography to secure communication between the tablet and the receiver and pairing them, requiring user acknowledgement before updating firmware, downloading of data such as maps & location using HTTPS or digitally signatures by the vendor.
We could only hope that the developers of these systems are taking note and performing the necessary measures required to secure these vital systems for casual pilots. Interested people can take a look at the <a href="https://cseweb.ucsd.edu/~savage/papers/CCS14MobileCockpit.pdf" target="_blank" rel="noopener noreferrer">PDF</a> submitted by the team. What are your thoughts on the new study? Share with us in comments below.
Source: #-Link-Snipped-#

