Software To Read Your Lips For Secure Authentication And Access - Mu'tah University
With fingerprint sensors only now entering our mobile devices, it's time for other secure authentication techniques to arrive in the latest software on our computers. Keeping up with fast pace in the security techniques development, Ahmad Hassanat from the IT Department at Mu'tah University in Jordan has come up with a software that reads the user's lips to authenticate him for logging into the computer. By making the machine learn how to analyze the pattern in lip & mouth movements, Hassanat could train the system to identify words being uttered correctly about 80% of the time.
In a paper published on this research work, Hassanat shares that the system is a two stage process - setting the visual password stage and the verification stage. By speaking the word into the camera, the system captures the video of the user's face and a words-based VSR system processes these words to extract a sequence of feature vectors. Later, when the user is trying to log-in, these features are compared with the stored visual password and the access is granted.
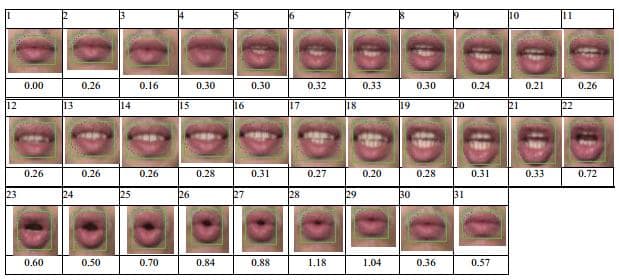
The appearance of mouth when uttering the word 'Zero'.
Ahmad Hassanat evaluated his system with a video database of 10 males and 10 females and found that system's feasibility is great and has the potential for practical approach thanks to error rate in the range of 7.63% to 20.51% at the worst tested scenario. The author of the paper claims that this new form of visual password would be the newest way for biometric security as even the best of actors would not be able to exactly mimic someone else's lip movements.
What would be the disadvantages of such a system? Let us know your thoughts in comments.
Source: <a href="https://gssrr.org/index.php?journal=JournalOfBasicAndApplied&page=article&op=view&path[]=1727" target="_blank" rel="noopener noreferrer">International Journals: Publishing Research Papers in all Fields</a>

