Security Researcher Finds OnePlus Phones Sending Personally Identifiable Data To Company
@satya-swaroop-YDeBJM
•
Oct 26, 2024
Oct 26, 2024
1.5K
OnePlus, came into limelight when it started its product range offering flagship devices at mid-range rates. It achieved the underdog status when it competed in the performance game with other flagships from companies like Samsung. Today however we found that there is a dark side of the company which constantly tries to up its game with every new smartphone. Software engineer Christopher Moore has found out that the company has programmed its phones to send out personally identifiable analytics data to its servers. While analytics data has been a staple for tech companies since existence, OnePlus phones sending out personal information like phone’s IMEI number and phone number are a bit disconcerting.

This discovery was made my Moore while competing in a hack challenge back in 2016. He monitored information being sent by an OnePlus 2 phone with the help of a security tool for attacking web applications called OWASP ZAP. Among the information being sent by the OnePlus 2, he found out that a lot of information was being sent to a domain called open[dot]oneplus[dot]net. He decided to investigate further and found out that it was an Amazon AWS instance owned by OnePlus. Using this tool and the encryption key stored on the OnePlus 2 he managed to decipher the exact information that was being sent.
Like most companies OnePlus was collecting information about abnormal restarts which is standard practice for developers to help them sort out bugs but he found the collection of phone data such as screen on and off and lock unlock a bit excessive. He decided to run the program for a bit longer and found out that the phone was sending sensitive personal information such as IMEI number, phone numbers, MAC addresses, mobile networks information and the serial number. While other companies collect analytics data they do so anonymously. For example when Google collects your location it cannot identify from its side the actual person it was taken from. OnePlus with this data can easily pinpoint the person using its phones.
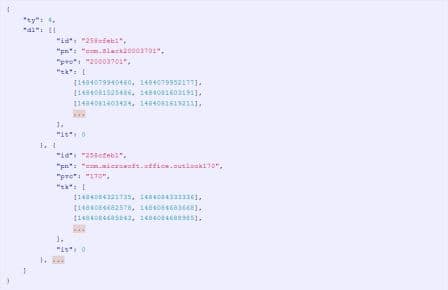
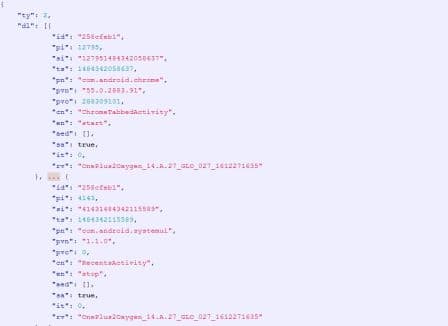

Snippets of findings
Furthermore OnePlus was even keeping track of your app use locking it down to the millisecond also along your personal information such as the phone serial number. They could even tell if you open a new tab on Google Chrome narrowed it down to the millisecond which is intrusive. He tried to convey this to OnePlus but was met with the usual troubleshooting approach. When Android Police covered his discovery they managed to obtain a reply from OnePlus. OnePlus said that the analytics were being sent to an Amazon server through a secure HTTPS channel and it helps them fine tune their software. They said that a bulk of this analytics information can be turned off by excluding from the User Experience Program. One Twitter user pointed out it was be stopped completely by removing the OnePlus Device Manager app without root via Android Debug Bridge by using your computer. We however would not recommend the second solution because it would hamper some features of your OnePlus phone.
Source: <a href="https://www.chrisdcmoore.co.uk/post/oneplus-analytics/" target="_blank" rel="nofollow noopener noreferrer">www.chrisdcmoore.co.uk</a> via #-Link-Snipped-#

This discovery was made my Moore while competing in a hack challenge back in 2016. He monitored information being sent by an OnePlus 2 phone with the help of a security tool for attacking web applications called OWASP ZAP. Among the information being sent by the OnePlus 2, he found out that a lot of information was being sent to a domain called open[dot]oneplus[dot]net. He decided to investigate further and found out that it was an Amazon AWS instance owned by OnePlus. Using this tool and the encryption key stored on the OnePlus 2 he managed to decipher the exact information that was being sent.
Like most companies OnePlus was collecting information about abnormal restarts which is standard practice for developers to help them sort out bugs but he found the collection of phone data such as screen on and off and lock unlock a bit excessive. He decided to run the program for a bit longer and found out that the phone was sending sensitive personal information such as IMEI number, phone numbers, MAC addresses, mobile networks information and the serial number. While other companies collect analytics data they do so anonymously. For example when Google collects your location it cannot identify from its side the actual person it was taken from. OnePlus with this data can easily pinpoint the person using its phones.
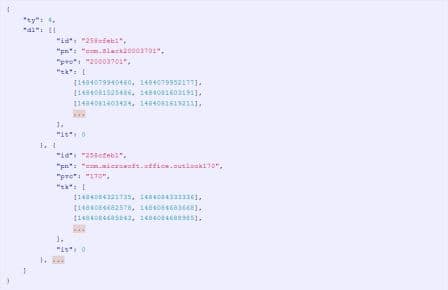
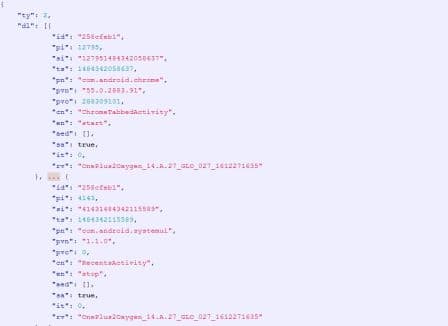

Snippets of findings
Furthermore OnePlus was even keeping track of your app use locking it down to the millisecond also along your personal information such as the phone serial number. They could even tell if you open a new tab on Google Chrome narrowed it down to the millisecond which is intrusive. He tried to convey this to OnePlus but was met with the usual troubleshooting approach. When Android Police covered his discovery they managed to obtain a reply from OnePlus. OnePlus said that the analytics were being sent to an Amazon server through a secure HTTPS channel and it helps them fine tune their software. They said that a bulk of this analytics information can be turned off by excluding from the User Experience Program. One Twitter user pointed out it was be stopped completely by removing the OnePlus Device Manager app without root via Android Debug Bridge by using your computer. We however would not recommend the second solution because it would hamper some features of your OnePlus phone.
Source: <a href="https://www.chrisdcmoore.co.uk/post/oneplus-analytics/" target="_blank" rel="nofollow noopener noreferrer">www.chrisdcmoore.co.uk</a> via #-Link-Snipped-#

