“Fake Cell Phone Towers Are Eavesdropping On Your Calls” Claim Makers Of CryptoPhone 500

Goldsmith uncovered these phony towers with the help of his CryptoPhone 500. The CryptoPhone 500 is a heavily modified Samsung Galaxy SIII that eliminates 468 vulnerabilities found on the stock software installation by employing sophisticated encryption system. When a CryptoPhone 500 comes across one of such fake cell phone towers it sends out the following warning messages to the user.
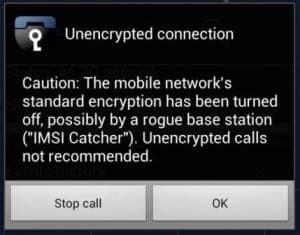
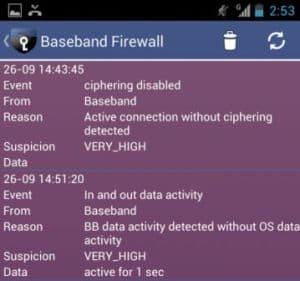
Warning Messages on a CryptoPhone 500

Suspected Locations of Phony Cell Towers
Various customers have received such warnings and the company has compiled a list of all the locations in the map above. Goldsmith tested his CryptoPhone by taking a drive near a government facility in Nevada and his phone was able to warn him about the threat. An iPhone was oblivious to the threat and an off-the-shelf Samsung Galaxy S IV went from a 4G to a 3G connection and back to 4G again. The CryptoPhone too was being forced to change from 4G to 2G. So now the obvious question arises, who is behind these attacks? The team at ESD America say that they haven’t been able to pinpoint the perpetrators. The suspect list consists of government and private entities that have the financial capability of procuring these interceptors which cost no less than $100,000.
Before concluding we would like to ask our forum members to go through the source link below and discuss these claims.
Source: #-Link-Snipped-#
