Apple Steps Ups Security With 2-Step Authentication For iMessage And FaceTime
Apple Inc. has added a layer of security of its messaging and video-conferencing apps- iMessage and FaceTime. The company has introduced 2-step authentication process for user security. Apple’s 2-step security is already in place for iCloud service that lets users save photos on cloud that is now n to above mentioned services as well. Two-step security is an extra-security feature for Apple ID that prevents any unauthorised user to access account, even if password is known. In short, it is a way to keep Apple ID and personal information as secure as possible.
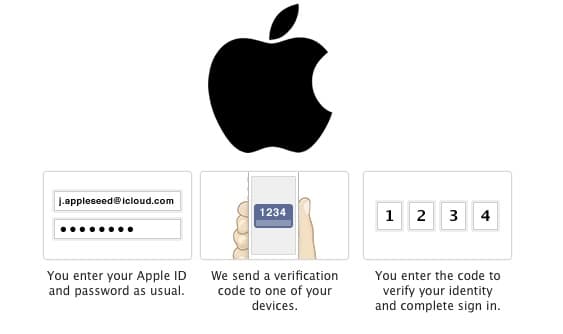
With 2-step verification, user can register mobile number of their device which would be used for sending authentication codes while sign-in. For signing-in, user need to enter Apple ID and password, along with a code that is sent on registered mobile number. The company will then verify the code and authenticate the user granting access. Apple has also introduced a 14-character code that can be issued in case the user loses the registered device to regain the access of the account.
It is believed that Apple is leaving no stone unturned to maintain users’ privacy and prevent hacks. Introducing two-step authentication is one way of doing so. It is worth noting here that earlier, several celebrity iCloud accounts were hacked and photos were leaked online. Even though 2-step authentication is kept optional, we believe that users’ should take advantage of it to ensure full security of personal information and other details to prevent its misuse by any unauthorized person or service.
Read more on how to use 2-step authentication on Two-step verification for Apple ID - Apple Support.
Via tech.firstpost.com
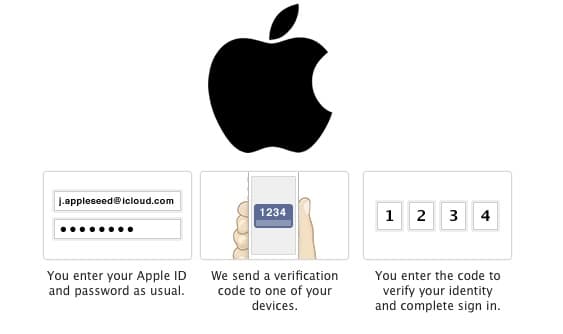
With 2-step verification, user can register mobile number of their device which would be used for sending authentication codes while sign-in. For signing-in, user need to enter Apple ID and password, along with a code that is sent on registered mobile number. The company will then verify the code and authenticate the user granting access. Apple has also introduced a 14-character code that can be issued in case the user loses the registered device to regain the access of the account.
It is believed that Apple is leaving no stone unturned to maintain users’ privacy and prevent hacks. Introducing two-step authentication is one way of doing so. It is worth noting here that earlier, several celebrity iCloud accounts were hacked and photos were leaked online. Even though 2-step authentication is kept optional, we believe that users’ should take advantage of it to ensure full security of personal information and other details to prevent its misuse by any unauthorized person or service.
Read more on how to use 2-step authentication on Two-step verification for Apple ID - Apple Support.
Via tech.firstpost.com
Replies
You are reading an archived discussion.
Related Posts
Sir i wanna know about the weight mechanism used in lift. how its sensors work when lift is overloaded............
Project Abstract / Summary : Data mining has become a hot research domain in recent years as it is being used in almost all applications. There are many algorithms under...
Project Abstract / Summary : MODIFICATIONS FOR THE IMPROVEMENT OF THE PERFORMANCE OF VORTEX TUBE
Vortex tube is a simple energy separating device which is compact and simple to produce...
Last year, NASA had announced its proposal to develop a conceptual design of a possible submersible autonomous vehicle (submarine) for performing autonomous detailed scientific investigations of the liquid methane/ethane seas...
Project Abstract / Summary : Our plan is to make a fighter jet which would have 2 special uses. They are:-
• Fast means of transport for military purpose.
•...
